8 Things You and Your Company Needs to Know About Cyber Security
An essential part of protecting valuable data is understanding cybercrime, especially when this data involves important business or organisation affairs. Cyber hackers have a variety of motives when hacking into networks, most often they look for financial gains through bribes, identity fraud or credit card information. These attacks can cost firms dearly as the hackers will take sensitive information then sell them on to the deep web where crime is hidden. To help protect data and stay alert against these attacks, businesses can imply solid network security protocols, this will keep information secure now as well as in the future.
Data theft is responsible for nearly 80% of all unauthorised network attacks. Most of the time, cyber security experts are unsure of the methods that hackers leverage when infiltrating into computer networks, but here are some common methods that we see often:
Account Hijacking – This can occur when a hacker breaks into a cloud-based service or database.
SQLi attacks – This is when a cyber-criminal delivers malicious codes which will take over a network database.
Distributed Denial of Service Attacks (DDos) – This is when an automated program directs so many pirated computers to request a website that no one can reach.
Malvertising – This will look like an advertisement but when someone clicks on it, it will deliver malicious codes.
It All Comes Down to Money –
A recent report showed that a lot of hackers sell an estimate of one trillion dollars, which was from stolen data. In May 2015 there was an investigation on the deep web which results in the confiscation of $80,000 in bitcoins.
Cyber Criminals Love Credit Cards –
It has become increasingly popular for criminals to steal debit and credit cards directly from ATM users, this trend has resulted into a lot of retail stores denying gift card purchases with credit or debit cards as they are easy to trace and monitor.
90% of the Internet is Not Invisible –
A lot of cyber criminals operate on a hidden network called the Darknet, within this they use very specific browsers so they don’t use a digital footprint. They also leverage other Darknet offerings like private databases, corporate networks and password protected sites.
Cyber Attacks Costs Businesses Lots of Money –
A university calculated that cyber-crimes cost around $300 billion annually, firms don’t even detect all of 70% of cyber intrusions.
IoT & Cyber Security –
The Internet of Things (IoT) industry is projected to boom. Apparently by 2025 experts are saying that there will be an estimate of 20.8 billions of IoT technologies in use. Although smart technology will make life easier for consumer5s and businesses, it is important to keep in mind that the cyber security risks that it could create.
Businesses Can Prepare for Attacks –
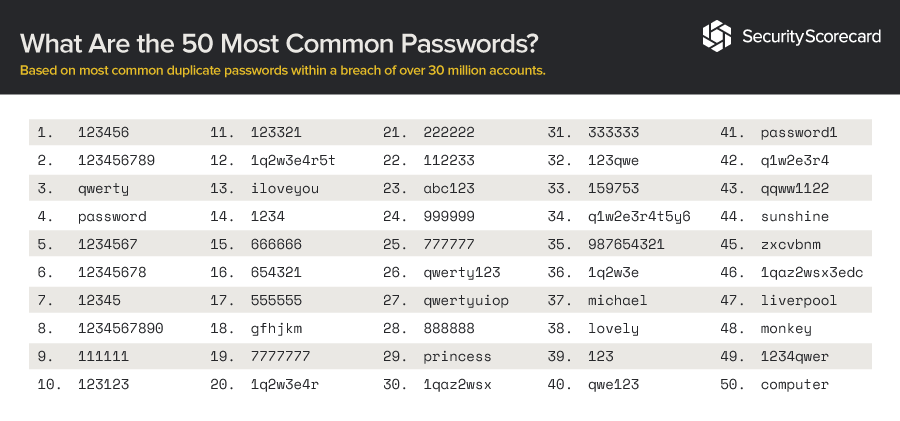
Training you staff so they are prepared for these attacks are really important if your company relies heavily on cyber communication. Also make sure you brief staff members on areas that are vulnerable to attacks, like Wi-Fi networks, mobile devices and passwords.
Cyber Security is an Ongoing Effort –
It might be a good idea to install a security continuum. Before an attack take the time to identify the normal network activity, then when an attack occur you will have the knowledge of typical activity which makes it easier to locate the attack vector and identify ways to improve future security measures.
New Threats May Arise –
Cyber attackers will continue to develop their hacking techniques as well as leverage complicated intrusion techniques. The can be things such as ghost ware which is a code that infiltrates a network, steals data then hides it presence. It is predicted that cyber hackers will develop methods to use cellular location-based information, and scareware which is a software designed to appear as though it is a solution for issues that don’t exist.