How to Enhance your Cyber Security Strategy
There has been a massive spike in online criminal activity and hackers this past year, the better your technology, the bigger the threat of ransomware or information threat for your business. a lot of businesses are now dependent on their computer systems, even though they have been designed to be fool-proof, there are still opportunities for human error and other vulnerabilities.
You need to pay attention to data security of your businesses systems, recently a lot of businesses have started to invest in separate cyber security teams that will monitor and protect the businesses network.
Even if you have the best cyber security team, you still need to have working processes and protocols in place to enhance the teams security measures and to protect your businesses information.
Here are some of the key strategies to make sure your data is safe:
Update your Systems
SaaS (Software as a Service) is getting more popular for smaller businesses, they have started to move their activities onto software platforms. You might have started to use software services like enterprise resource management inventory management, workforce scheduling or database management, these need to be regularly updated to keep the security that is protecting them up to date. If you constantly update your systems, then your business will always stay one step ahead of the hackers.
Train your Employees
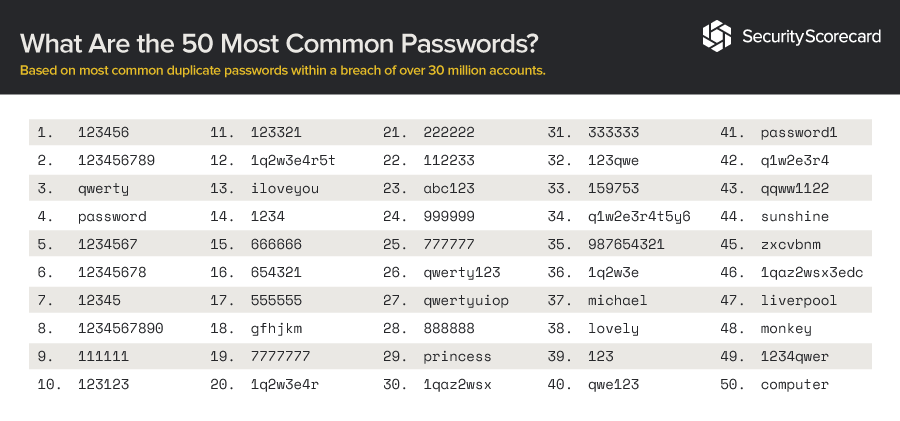
It is now vital to make sure your employees are aware and have the knowledge of cyber security and how to protect your businesses data. If you employees are using the software systems stated above, they need to be aware of the vulnerabilities and what to do if a threat happens. You need to make sure that your employees are also aware of the variety of cyber-attacks and malware.
Ensure Security Protocols
One of the main things that you need to do to attain high levels of data security is to create clear protocols for access and operation. Your employees need clear guidelines on how to access their work, sources of data and how to communicate with each other and clients. You will also need to have systems put in place to make sure your employees stick to these protocols. One of the most dangerous cyber security attacks is social-engineering, your employees will need to recognise this if they are talking to someone over the phone or when someone is pretending to be new personnel. You need to have clear identity confirmation protocols in place and your employees must know what to do if this happens.