How to Protect Data on your Employees’ Devices
Company owned and personal devices are synchronised with the corporate network. The business information will be data files, calendar entries, clients, suppliers, colleagues. This synchronisation enhances employee productivity as they can walk on behalf of the company whenever and wherever they want, but this also means that your employees will also have access to sensitive information that you could lose if the employee stops working with you
To avoid problems like this happening then you need to enforce a strict BYOD (Bring Your Own Device) policy. Your employees must be aware of the amount of personal and sensitive information they have access to. Here are some tips on how you can protect data on your employees’ devices:
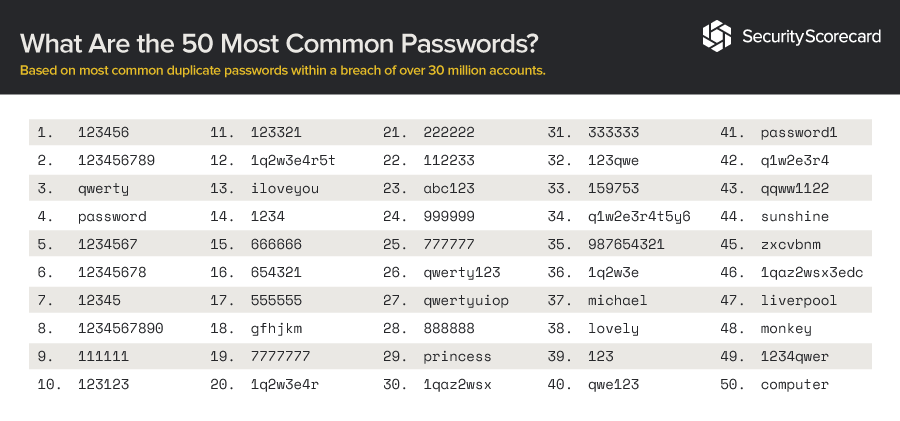
All BYOD devices must have a strong password, it must contain capital letters, lowercase letters, numbers and symbols if possible. BYOD devices must also lock automatically.
Transfer data securely to prevent third-party access via an encrypted channel. The data needs to be encrypted at all times using a reliable encryption software.
When using something like a USB stick to transfer data, make sure that all the data is removed from the USB stick after the data has been transferred over.
Always use a secure Wi-Fi connection when accessing data.
Do not download untrusted apps to any BYOD device, untrusted apps post a threat to the security of the data held on your device.
Do not retain personal data on your devices for longer than necessary, unless you need to for legal reasons.
Sometimes deleted data is stored in a recycle bin or waste management system, make sure that all data is permanently deleted.
Before you leave the business make sure all work-related data is deleted from your device, before your last day.
To comply with new data protection rules, businesses must use mobile device management software, this software will allow devices to be configured and managed remotely. If a device that is protected with the mobile device management software was to ever get stolen or lost, then the data will be able to be wiped clean remotely.